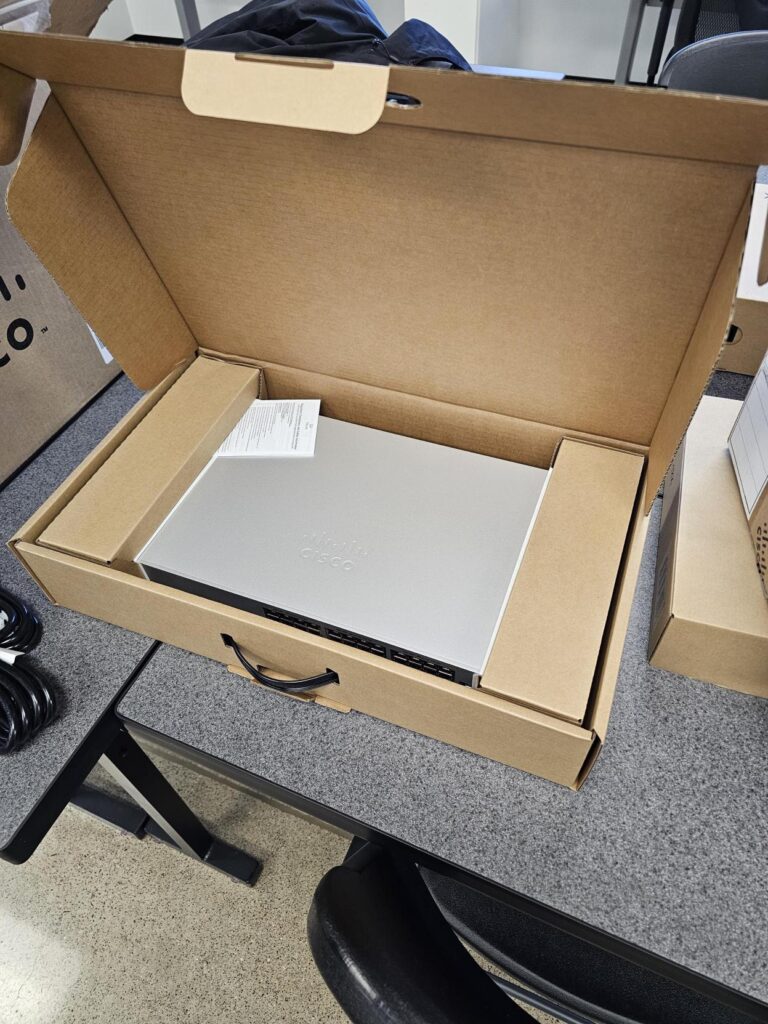
When your brand-new Cisco switches arrive looking like they’ve been to a few parties without you, it’s not just an unboxing disappointment—it’s a supply chain red flag that could compromise your entire infrastructure.
Let me tell you about a recent situation that perfectly illustrates why “trust but verify” isn’t paranoia in cybersecurity—it’s basic operational hygiene.
The Scenario: Critical Infrastructure Meets Questionable Packaging
We recently ordered Cisco Meraki MS130-12X switches for a customer in waste management—a sector that falls squarely into the critical infrastructure category. These weren’t lab toys or homelab upgrades. This was production equipment destined for systems that keep essential services running.
The switches came through authorized distribution channels. They were sold as new. Shipped directly from Cisco. Everything checked the right boxes on paper.
Then the boxes arrived.
And those boxes? Already open.
No tamper-evident seals. No anti-static bags protecting $2,000+ networking equipment. One switch showing visible cosmetic scuffing that suggested it had seen some action before landing on our loading dock.
For equipment headed into a production environment supporting critical infrastructure, this isn’t a minor packaging oversight. It’s a fundamental breach of supply chain integrity.
Why Factory-Sealed Actually Matters (Spoiler: It’s Not About Aesthetics)
Here’s where some folks might think we’re being precious about packaging. After all, if the switch works, what’s the big deal?
The big deal is that networking equipment isn’t like buying a toaster on Amazon.
Network switches sit at trust boundaries. They forward traffic. They inspect packets. In many environments, they terminate connections that support operational systems, safety systems, and regulatory compliance frameworks. When that switch has an unclear provenance, you’re essentially plugging a question mark into the foundation of your security architecture.
For new enterprise networking equipment—especially from tier-one vendors like Cisco—there are baseline expectations that aren’t negotiable:
- Factory-sealed packaging that hasn’t been previously opened
- Tamper-evident protection that shows if someone’s been inside
- Anti-static bags (because electrostatic discharge is still a thing)
- Clear chain-of-custody indicators from factory to customer
When those protections are missing, you lose the ability to confidently verify the equipment’s history. And in critical infrastructure environments, “probably fine” isn’t an acceptable risk posture.
Greyware: It’s Not Just About Unauthorized Resellers Anymore
Most people think of greyware as equipment sold outside authorized channels—the stuff you find on sketchy marketplaces or through too-good-to-be-true dealers. That’s absolutely part of it.
But greyware also includes hardware that’s been previously handled, staged, deployed for demos, returned, or reintroduced into inventory without proper disclosure—even when it moves through authorized distribution channels.
The term “new” has become dangerously flexible in IT procurement. Equipment can be:
- Pulled for internal testing then resold as new
- Used in proof-of-concept deployments then repackaged
- Customer returns that get “refreshed” back into inventory
- Evaluation units that somehow make their way back into the sales pipeline
When your equipment arrives open, unsealed, and improperly packaged, you have no reliable way to know which category applies. That uncertainty alone should disqualify it from production deployment in environments where security and reliability aren’t optional.
The Critical Infrastructure Context Makes This Worse
Let’s be clear about what “critical infrastructure” means in this context. We’re talking about systems that support essential services—in this case, waste management operations that directly impact public health and environmental safety.
These environments often operate under regulatory frameworks that require documented security controls, verified supply chain integrity, and defensible risk management decisions. Deploying networking equipment with questionable handling history creates audit exposure, compliance gaps, and operational risk that extends far beyond the IT department.
This wasn’t lab equipment. This wasn’t gear for a test network or a proof-of-concept deployment. This was production infrastructure supporting systems that communities depend on.
In these environments, even low-probability risks must be taken seriously. Accepting networking equipment with unclear handling history introduces avoidable uncertainty into the foundation of your security architecture—and creates downstream liability that’s difficult to quantify or contain.
What Happens When You Escalate (Spoiler: We’re Still Waiting)
We opened a case with Cisco. Their response: they’ll investigate and respond within five business days.
That’s where we are as of this writing—waiting for an explanation of how equipment sold as new arrived in a condition that raises obvious supply chain integrity questions.
To Cisco’s credit, they have a formal process for handling these situations. But the fact that this situation occurred in the first place highlights gaps in quality assurance and supply chain controls that shouldn’t exist for a vendor whose products routinely deploy in regulated and critical environments.
Here’s what customers reasonably expect when they buy new networking equipment:
- Factory-sealed packaging that hasn’t been previously opened
- Tamper-evident protections intact and uncompromised
- Proper anti-static protection for sensitive electronics
- Zero signs of prior handling, deployment, or wear
- Documentation that supports a clear chain of custody from factory to customer
These aren’t luxury requests. They’re baseline requirements for maintaining supply chain integrity in environments where trust is foundational to security.
The Uncomfortable Economics of Supply Chain Shortcuts
Let’s talk about why this happens—because it’s not usually malicious actors inserting backdoored switches into the supply chain (though that’s a real threat vector too).
More often, it’s economic pressure and operational shortcuts that normalize exceptions:
- Reverse logistics complexity: Returns get reintroduced into inventory to avoid write-offs
- Demo equipment recycling: Gear used for sales demonstrations gets repackaged and resold
- Channel inventory management: Distributors move equipment between locations and customers
- Quality control gaps: Inspection processes fail to catch improper packaging or handling
Each of these practices might make business sense from a cost-recovery perspective. But they systematically shift risk away from vendors and onto customers—who are left trying to determine whether their “new” equipment has an unknown history that could introduce security or reliability concerns.
The problem: When these practices become normalized, the definition of “new” becomes increasingly flexible. And customers lose the ability to confidently verify what they’re actually buying.
What You Should Do If This Happens to You
If you receive networking equipment sold as new and observe any of the following red flags:
- Opened or previously sealed packaging
- Missing or compromised tamper-evident seals
- Equipment not properly protected in anti-static bags
- Visible signs of prior handling, wear, or cosmetic damage
- Missing or incomplete documentation
- Serial numbers that don’t match purchase orders or documentation
Stop. Document. Escalate.
- Pause before deployment: Do not connect this equipment to production networks
- Document thoroughly: Photograph packaging, equipment condition, serial numbers, and any discrepancies
- Escalate through proper channels: Contact your vendor and the manufacturer
- Demand replacement: Accept nothing less than factory-sealed, properly packaged equipment
- Review your procurement process: Ensure your purchasing agreements explicitly define “new” and specify packaging requirements
Normalizing exceptions in the supply chain shifts risk away from vendors and onto operators—a trade that rarely favors the customer and never serves the security of critical infrastructure.
A Message to Vendors: Factory-Sealed Isn’t Optional
This isn’t an allegation of malicious activity or intentional fraud. But it is a reminder that supply chain integrity is a core component of security—not a nice-to-have feature or a box to check for compliance.

For networking equipment destined for critical infrastructure and production environments, “new” should always mean:
- Factory-sealed packaging
- Tamper-evident protections intact
- Proper anti-static protection
- Clear documentation of chain of custody
- Zero signs of prior handling or deployment
This standard isn’t arbitrary. It exists because customers need to confidently verify that their infrastructure foundation hasn’t been compromised—intentionally or otherwise—before it ever reaches their data center.
The Broader Implications for Cybersecurity
Supply chain attacks have moved from theoretical threat models to front-page news. From SolarWinds to malicious USB cables, the security community has learned that trusting hardware and software at face value is a recipe for compromise.
Network equipment represents a particularly attractive target for supply chain interdiction:
- Persistent access: Switches and routers operate 24/7 in trusted network positions
- Visibility: They see all traffic traversing the network
- Privilege: They often have access to management networks and sensitive systems
- Longevity: Network equipment typically stays in production for years
When that equipment arrives with compromised packaging or unclear handling history, you’ve lost the ability to confidently establish your security baseline. You’re essentially asking your team to build a fortress on a foundation you can’t verify.
What Success Looks Like
We’re still waiting for Cisco’s response. When it comes, we’ll update accordingly.
But regardless of how this specific situation resolves, the broader lesson stands: supply chain integrity for critical infrastructure isn’t negotiable.
Customers should expect—and demand—that equipment sold as new arrives in factory-sealed condition with clear chain-of-custody documentation. Vendors should implement quality controls that make exceptions impossible, not just unlikely.
And when gaps appear, escalating loudly and refusing to normalize the exception protects everyone: customers who depend on secure infrastructure, vendors whose reputations depend on trust, and the broader ecosystem that relies on supply chain integrity as a foundational security control.
Because in critical infrastructure and security work, trust in the supply chain isn’t optional. It’s foundational.
Have you experienced supply chain integrity issues with networking equipment?
Share your experiences with us because the more we talk about these situations, the harder it becomes for vendors to treat them as acceptable exceptions rather than fundamental failures.
Want help evaluating your infrastructure supply chain security? Contact IT Audit Labs to discuss how we help organizations verify that their “new” equipment actually means factory-sealed.