Microsoft Vulnerabilities: How to Measure Progress With a Growing Code Base
How we got here In the early days of software development, security was an afterthought. Protocols like HTTP, FTP, and Telnet were created with little
Stay informed with expert insights from IT Audit Labs.
Our blog explores the latest in cybersecurity, compliance, and risk management, breaking down complex topics into actionable guidance. Whether you’re an IT leader, security professional, or business decision-maker, you’ll find timely updates, in-depth analysis, and practical tips to help you stay ahead of emerging threats and evolving industry standards.
How we got here In the early days of software development, security was an afterthought. Protocols like HTTP, FTP, and Telnet were created with little

After a year of hands-on testing, security engineer Cameron Birkland shares what he’s learned about the Flipper Zero—a powerful wireless hacking tool making waves in cybersecurity. From cloning garage remotes to launching BLE attacks, this guide explores Flipper Zero’s capabilities, firmware upgrades, accessories, and why it’s both a valuable learning device and a rising concern for physical security.

VPNs are essential tools for online privacy, but they’re not without risks. In this blog, cybersecurity expert Nick Mellem breaks down how VPNs work, common pitfalls, and the best practices to keep your data secure—even when your VPN isn’t.

In today’s digital world, storing data is more important than ever. We’ve come a long way—from punch cards and magnetic tapes to hard drives, flash
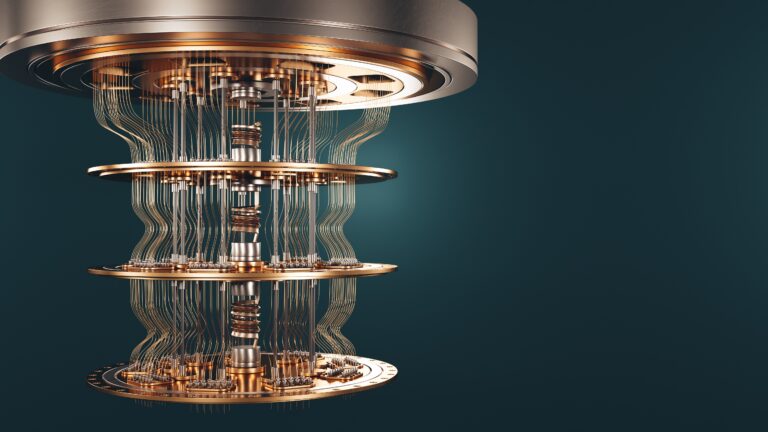
Quantum computing flips the switch on classical bits—using qubits that exist in multiple states simultaneously—to tackle problems at unprecedented speed. From accelerating drug discovery and powering next‑generation AI models to posing new challenges for today’s encryption, quantum tech is poised to redefine industries. In our chat with expert Bill Harris, we break down the fundamentals, explore real‑world applications, and discuss how innovators like IBM and leading nations are racing toward a quantum future.

In today’s hyperconnected world, keeping your personal data secure is more important than ever. In our recent episode of The Audit, we unpacked the hidden

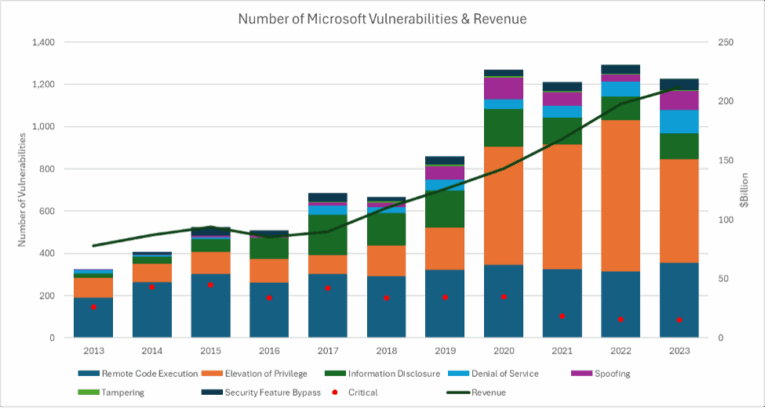
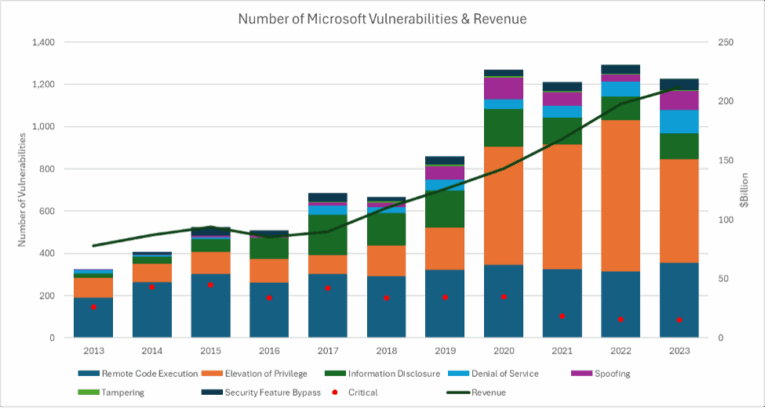
As software development accelerates, overlooked vulnerabilities multiply—and threat actors are ready to exploit them. From malicious macOS toolkits to stolen ChatGPT credentials, today’s risks demand a balance between timely updates and system stability. By patching promptly, using trusted security suites, and layering defenses like password managers and antivirus tools, you can navigate this golden age of data breaches with far less exposure.

From mental arithmetic to affective computing, artificial intelligence is reshaping every industry. Rather than banning chatbots, forward‑thinking leaders empower teams to draft reports, automate routine tasks, and refocus on strategic work. Meanwhile, creative AI—whether composing music with GANs or generating novel game strategies like AlphaGo—raises new questions around copyright, emotion, and human–machine collaboration.

Packing your toothbrush is crucial—but so is securing your devices and data. Beware ‘too good to be true’ travel deals, lock down gadgets in a portable safe, and avoid auto‑connecting to public Wi‑Fi without a VPN. Delay real‑time social media posts to keep your whereabouts private, and always enable two‑factor authentication on critical accounts.